
The JavaScript library downloaded by 100 million developers worldwide each week has been quietly contaminated. Google Threat Intelligence Group (GTIG) announced on March 31 that malicious code was found in two versions of the axios package distributed in the NPM ecosystem. Once installed, a backdoor is set up. It is difficult for developers themselves to detect.
The problem versions are 1.14.1 and 0.30.4, with weekly downloads reaching 100 million and 83 million respectively. The attacker hijacked the axios administrator account and secretly inserted a malicious dependency package called ‘plain-crypto-js’. This structure exploits the ‘postinstall’ hook that NPM automatically executes right after package installation to plant a backdoor without user intervention.
GTIG analyzed this attack as the work of UNC1069, a North Korean-linked hacking group for financial gain. Active since 2018, this group introduced the advanced version of existing malicious code, WAVESHAPER.V2, for this attack.
It infects regardless of Windows, macOS, or Linux and sends signals to the attacker’s server every 60 seconds, waiting for remote commands.
Infection path, this is how they infiltrate
The attack method is cunning. The installation script itself is obfuscated, making it difficult to determine what actions it performs even if you look at the code. It hides key commands and server addresses using XOR and Base64 combinations. After execution, it attempts to delete itself to erase traces.
The payload differs depending on the operating system. On Windows, it copies a legitimate file, PowerShell, under a different name and executes it in hidden mode.
On macOS, it downloads an executable file to the system cache path and runs it in the background.
On Linux, a Python-based backdoor settles into a temporary directory. In all three cases, after installation, the changes made in package.json to indicate infection are reverted to their original state to avoid detection.
Once a backdoor is installed, the attacker gains significant privileges. They can collect system information, browse directories, execute arbitrary scripts, and inject additional executable files. On Windows, registry entries are added to survive a reboot.
What actions to take immediately
Checking for infection is the first step. Open the lock file (package-lock.json or yarn.lock) of the project and look for the ‘plain-crypto-js’ item. If version 4.2.0 or 4.2.1 is present, it should be considered an infected environment. Utilizing dependency audit tools such as Wiz or Open Source Insights can allow you to verify dependencies in one go.
Version control is the second step. Immediately stop using axios 1.14.1 and 0.30.4. The safe versions are 1.14.0 and below, and 0.30.3 and below, respectively. Explicitly pin these versions in package-lock.json to prevent accidental upgrades. If your company operates an internal NPM repository, you must promptly adjust the settings to ensure that infected versions are not served.
Temporarily halting the CI/CD pipeline is the third step. Stop all build and deployment processes that include packages dependent on axios. If your settings still automatically fetch the ‘latest version’, this is an opportunity to remove it. Explicitly pin safe versions and redeploy.
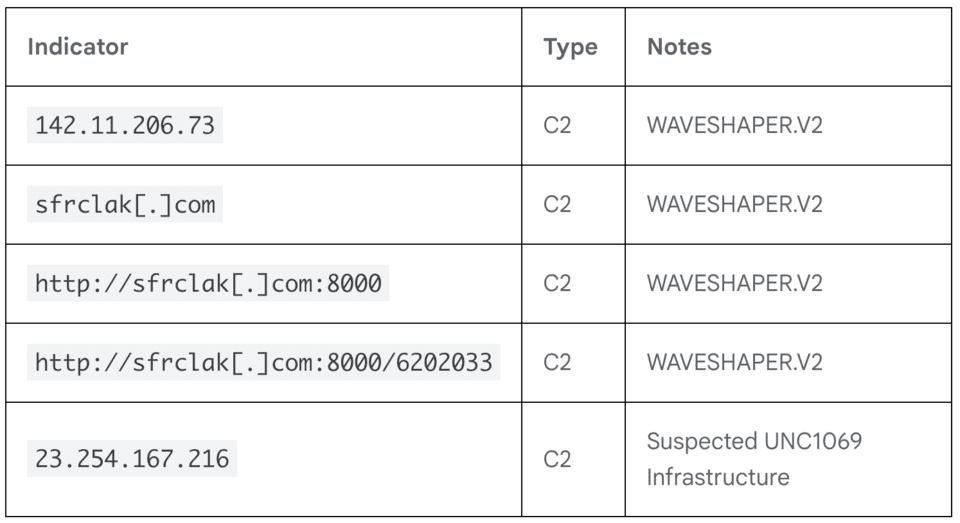
Network blocking is a measure that can be immediately executed. Block all traffic heading to the attacker’s infrastructure, domain sfrclak[.]com, and IP address 142.11.206.73 at the firewall. If there is an already infected terminal, it may be attempting to communicate with this address at 60-second intervals.
If infection is confirmed
The principle is to consider an environment where plain-crypto-js is found as entirely compromised. Isolate that environment and restore it to a known clean state. Next, replace credentials. Change all API keys, tokens, and access passwords used in the affected environment. You must respond based on the premise that exposure might have occurred from the moment the backdoor was installed.
You also need to delete local and shared caches of NPM, yarn, and pnpm. If infected files remain in the cache, there is a risk of reinfection during subsequent installations. Both developer workstations and build servers are targets.
If you lack endpoint detection and response (EDR) solutions in your development environment, now is the time to consider implementation. Patterns of abnormal child process creation from the Node.js process are key behavioral indicators in this attack. Applying the YARA rule disclosed by GTIG to build servers and developer endpoints can aid in post-detection.
In the long term, isolating the development environment itself using containers or sandboxes is recommended. The habit of storing sensitive credentials in plaintext within code or environment variables was a target point of this attack. Transferring them to an OS keychain or secure vault is a fundamental remedy.
The key revelation of this incident is that trust in the open-source ecosystem was a vector of attack. Even packages like axios, believed to have been verified by hundreds of millions, can instantly become weapons if just one administrator account is breached. Fixing versions and routinely auditing dependencies is the most practical defense currently required for developers.